Antiviruses and security updates do a fantastic job of protecting a computer from malwares, but they can only function when the operating system is running. But what if the malicious code gets loaded before the operating system has finished booting? For such circumstances secure boot was developed. Secure boot is an additional layer of security that verifies that the program being loaded during the boot process is trusted. It does so by using checksums and cryptographic signatures. Secure boot is a feature of UEFI firware. Now, what is UEFI?
Unified Extensible Firmware Interface
UEFI stands for Unified Extensible Firware Interface. It is the modern and most widely used specification, and acts as an interface between operating systems and the system firmware. The system firmware contains instructions for the boot process. UEFI replaced the legacy BIOS firmware interface, but it is backward compatible with it. We won’t go deep into the the boot process, as the aim of this blog is to understand how secure boot, a feature of UEFI, works.
Signing Keys
So secure boot prevents malicious code from running on a PC by only allowing trusted operating systems to boot, but how does it know which operating system to trust? This is achieved by certain ‘keys’ that are enrolled into the firmware, that help in identifying the operating system. For example, most of the OEMs ship Windows Pcs with Microsoft keys, due to which, only Windows operating systems, like Windows 8, Windows 8.1, Windows 10 and Windows 11 can boot when Secure Boot is enabled. Note that Windows 7 does not support secure boot, and hence will not boot with it enabled.
The Enemy of Multi Boot
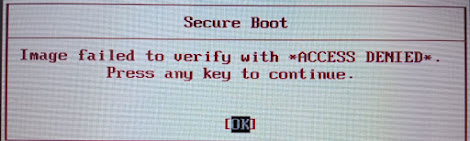
For most users, secure boot is just another setting in their UEFI firmware. In fact, most users don’t even know how to enter into the firmware settings of their device. The most common reason for changing the Secure Boot setting is multi booting, i.e., installing more than one operating system. Initially, most Linux distributions did not support secure boot, at least not as well as Windows. Even today, only major Linux distributions like Ubuntu, Fedora, OpenSuse, Debian etc support secure boot out of the box. These distributions use a software package called ‘Shim’ to become ‘trusted’ for secure boot. Each of these distributions develop their own version of Shim, and need to get it signed by Microsoft.
For other distributions, you need to disable secure boot in your device’s firmware settings before booting up the installer. After installation, you can manually configure Shim to get your system to boot with secure boot enabled, by signing the binaries yourself, but it does take a bit of work, and most users would rather prefer to just disable secure boot.
The Interesting Case of Windows 11
When Microsoft announced Windows 11 in June 2021, it eliminated a lot of modern computers from the eligibility list by having 8th generation Intel processor as the minimum requirement. AMD users weren't as severely affected as most AMD laptops were released only in recent years. But processor wasn't the only requirement that was bumped up. Windows 11 also requires a secure boot capable PC. The announcement created a lot of confusion initially, with many believing that Windows 11 won't boot without secure boot enabled, but it turns out that secure boot just needs to be present, and doesn't have to be enabled for Windows 11 to function.
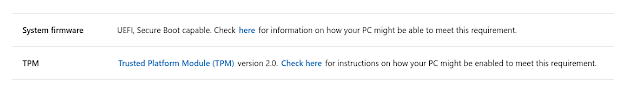 |
| Microsoft support website, showing the updated security requirements for Windows 11 |
The requirement is a part of Microsoft's decision to make Windows 11 more 'secure' than Windows 10. Since legacy BIOS systems are not supported anyway, most systems released after 2013 should have UEFI and secure boot. Computers with 7th generation and lower Intel processors can be updated to Windows 11 using method given by Microsoft on their website, given that they are UEFI and secure boot capable.
Ending Notes
Secure boot is definitely not a useless feature of UEFI, and does reduce the risk of malware attacking your system before booting, but if you need to, you can easily disable it. For now, no OEM is forcing the users to keep secure boot enabled.
Contact me on LinkedIn






0 Comments