In this
world where technology is advancing day by day have you ever wondered how many
mobiles or tablets is currently been connected to the internet? Of course, the
answer would be in millions since mobile phones or laptops are being used by
people of all age groups and from all strata of life. But have you ever
wondered that despite millions of
people using the internet at the same time if we type youtube.com or amazon.in ?in we
get our desired results in front of our screen. How does the internet gives us the desired and accurate result of our search when millions of devices are connected?
If you are confused and trying to seek answers to all the above questions let us dive into and get introduced to the concept of IP address.
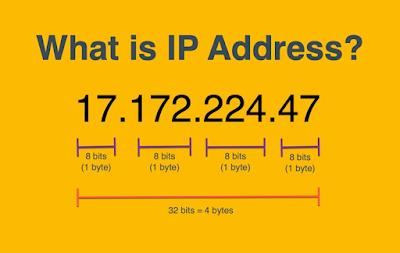
What is an IP address?
The IP address is designed to allow one connected
computer to communicate with another
device over the internet. IP addresses allow literally billions of digital
devices connected to the internet to be pinpointed and differentiated from all
the other devices. The “IP” part of the IP address stands for “Internet Protocol.” and the “address” part refers to a unique number that gets linked to all online
activity you do. Each IP address is unique.
How this IP address works
Your computer is indirectly connected to the internet via a
network that is connected to the internet itself or grants you permission to
connect to the internet. At home, this network
will be your ISP (Internet Service Provider), at work, it would be your office network. This IP address is just like the mailing address on the
letter. The postman knows where to deliver this letter because of the mailing
address mentioned on it. Since our ISP provides us an IP address when we search the internet sends the desired results to our IP address.
This IP address does not remain the same. If we connect to a public network in a café our device will be provided with a different IP address and not the one provided by the ISP at our home.
Your IP holds certain information about you. People can find and use
it for their purposes.
What can happen if your IP address fell into wrong hands?
- Your IP can be blacklisted on a particular website. After blacklisting, you will not be able to open that website.
- Your IP can become a mask for the Hacker. The hacker can use or replace your IP to do cyber crimes. And the Police arrest you as they found your IP while doing that crime. By this, the Hacker can save himself and make you trouble.
- A hacker can hit you with a DDoS (Distributed Denial of Service attack). A DDoS attack uses an army of computers controlled by a hacker to flood your device with traffic so it disconnects from the internet and completely shuts down.
- Someone can use your IP to hack your device. The internet uses ports as well as your IP address to connect. There are thousands of ports for every IP address, and a hacker who has your IP can try all of those ports to brute-force a connection and can steal your information.
- Download and Install a VPN: A VPN or Virtual Private Network is a software service that encrypts all of the data sent to and from the internet and routes it through a VPN server in another location. The VPN server acts as a middleman between your device and the internet, so websites and online apps only see the server’s IP address and not your own. Some of the benefits of using a VPN are Changing your IP address and Powerful security encryption.
Use a proxy server: A proxy server also acts as a middle man between your device and the internet. The websites can see the IP address of the proxy server and not your IP address. In fact, a VPN is a type of proxy but VPN is superior to a proxy server due to these points.
Proxies run very slowly. This can be frustrating when trying to browse the web. Proxies don’t have security protocols. Proxies don’t encrypt your data. Proxies intercept user traffic per application only while a VPN will protect all data moving in and out of your entire system.
- Use TOR: TOR or commonly known as The Onion Router is a decentralized worldwide anonymity network operated by thousands of volunteers. It assigns you a brand new IP address just like the VPN does. It’s also called the dark web as it allows you to access websites that are inaccessible if you’re using a normal browser. When you connect to Tor, your internet traffic is encrypted and routed through a random sequence of these volunteer “nodes,” which are sort of like proxy servers. Websites can only see the IP address of the last server in the sequence, called the exit node. Each time you visit a website, the sequence of nodes changes. This makes it practically impossible to trace activity back to the original IP address.
- Connect to a different network: Whenever you change networks, your IP address changes as well. You can connect to a public or private WIFI network, or use your smartphone’s mobile data connection. But it does leave your data vulnerable to hackers. Therefore it is advisable to opt for a network which requires a password to gain access.
- Use a NAT Firewall to hide your private IP address: If you use a wireless router to connect to the internet, it’s likely that you’re behind a NAT firewall. In simplest terms, a NAT firewall allows multiple devices on the same network to use the same public IP address but unique private IP addresses. A NAT firewall doesn’t hide your public IP address, but your private IP address. All devices connected to a NAT-enabled router will share a public IP address.
- Unplug your modem to change your IP address: This isn’t guaranteed to work, but you can often get a new IP address by unplugging your internet modem and plugging it back in again. When you lose the connection to your ISP, your old IP address will get recycled. When you re-establish a connection, you’ll be assigned a new IP address. Your ISP must use dynamic IP addresses for this to work.





0 Comments