GIST ON DATA BREACHES
Data breaches may alter the direction of your life rather than just causing momentary dread. Sensitive information exposure can have serious repercussions for people, businesses, and governments. Hackers can access you via the internet, Bluetooth, text messages, or the online services you use, whether you are online or offline. Without proper precautions, a little flaw could result in a significant data breach. Many people don't pay enough attention to it since they are ignorant of how common current security dangers work.
You'll learn the answers to some frequently asked questions as we continue:
1.What are data breaches?
2.What causes a data leak?
3.How could I be impacted by a data breach?
4.How can I guard against data breaches?
What is a data breach?
A data breach is when private, sensitive, or protected information is made available to an unauthorized individual. In a data breach, the files are read, copied, or shared without authorization.
Any person, high-level corporations, or governments could be at risk of a data leak. More significantly, if they are not protected, anyone can endanger others.
Data breaches typically occur as a result of:
1.Technology.
2. User behavior.
There are more opportunities for data to be compromised as our computers and mobile devices gain more connected capabilities. Technology is developing faster than we can protect it. IoT devices are proof that we are beginning to prioritize convenience over security.
Hackers are taking advantage of the obvious security weaknesses in many "smart home" gadgets, such as the absence of encryption. We'll continue to see this issue get worse if digital goods, services, and tools are being used without adequate security testing.
HOW DATA BREACHES OCCUR?
When sensitive or confidential data is accessed without authorization or shared, a data breach occurs. Cybercriminals can do this physically or virtually by breaking into a data source and stealing the data. Malware, human mistake, social engineering, and criminal hacking are the most frequent causes of data breaches.

Cyberattacks lead to malicious data breaches, therefore you should be aware of what to look out for.
Here are a few common techniques used by hackers:
1.Phishing
2.Brute Force Attacks
3.Malware
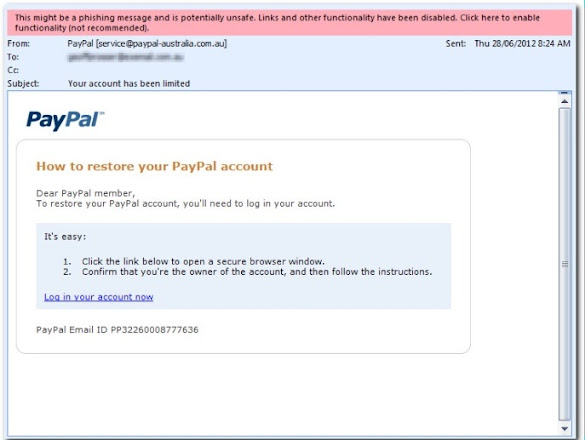
Phishing: The goal of these social engineering assaults is to trick you into allowing a data breach. To easily trick you, phishing attackers take the form of persons or organizations you trust. These kinds of criminals try to persuade you to give them access to sensitive data or to give them the data directly.
Brute Force Attacks: Hackers may employ software tools to try and guess your passwords in a more brazen manner. Although these attacks take some time, they are now happening more quickly as computer speeds increase. To hasten the process, hackers can infect other devices like yours with malware.
Malware: There may be security issues in the network and servers you're linked to, the operating system, software, and hardware on your device, and more. Criminals look for these security flaws because they make the ideal entry points for their software. Particularly spyware is great for collecting confidential information while remaining entirely undiscovered. This infection might not be discovered until it is too late.
19.81 billion records were made vulnerable last year as a result of improperly setup databases and lax security best practices. Threat actors scour the Internet constantly for exposed databases that are accessible to the general public through search engines and public-facing pages. These databases are frequently found by security researchers or threat actors who then publicize their presence on illegal forums since they frequently have weak password security or lack two-factor authentication. These in turn can have serious repercussions on many people for example: It can reveal your social security numbers, they can engage in all kinds of fraudulent acts under your name and can lead to identity theft and as Dwight K. Schrute quoted "Identity theft is not a joke Jim, millions of families suffer every year".
WHAT DO HACKERS TARGET FOR DATA BREACHES TO OCCUR?
During data breaches, hackers may target a variety of information. They can take your entire name, phone number, email address, and encrypted passwords. Additionally, they can try to log into other accounts that use the same email address and send spam using your email. Additionally, hackers may try to steal identities. Your name can be used to search your online footprint for other publicly available information about you. Your phone number may also be used for SIM-jacking, identity theft, and spam calls.
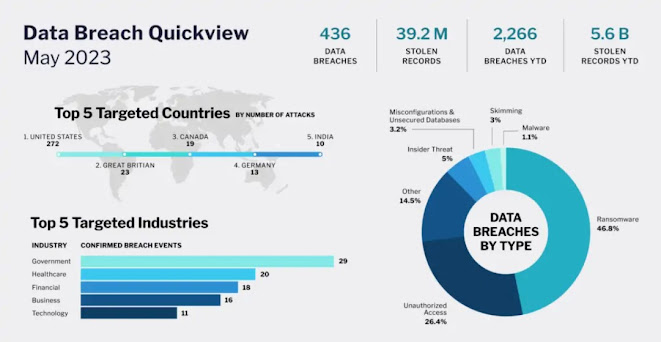
Government, retail, and technological businesses are the main targets of hackers. These industries may be their target because they frequently possess significant volumes of valuable data that can be sold or utilized to generate profit. For instance, retail businesses may hold credit card information or other financial data, government institutions may have sensitive information about residents or national security.
The following various types of information are frequently compromised in data breaches:
- Numbers from credit cards and other financial details.
- Contact details for customers, including names, addresses, and phone numbers.
- Information about employees, such as Social Security numbers and salary, businesses' trade secrets, or intellectual property, and medical records.
- government-issued identifying numbers, such as those on a driver's license or passport.
HOW TO PREVENT YOURSELF FROM BEING A DATA BREACH VICTIM?
Take preventative steps to safeguard your personal information if you want to avoid becoming a victim of a data breach. You can follow the instructions listed below:
- Use strong and unique passwords for all your accounts and enable two-factor authentication whenever possible. Your accounts are given an additional degree of security as a result, making it more challenging for hackers to access them.
- Make use of the most recent security patches and upgrades to keep your operating system and software current. This helps in addressing any weaknesses that hackers may try to exploit.
- When opening emails or clicking on links from unfamiliar or suspicious sources, use caution. Hackers frequently use phishing attacks to steal personal data.
- Regularly check your credit reports and financial accounts for any suspicious behavior. Report anything strange you observe right away.
- To shield your devices from malware and other risks, use trusted antivirus and firewall software.
- Limit the amount of personal information you post on social media or other open platforms and be careful what you disclose online.
- When using public Wi-Fi networks to access the internet, use a virtual private network (VPN) to encrypt your internet connection and protect your data from prying eyes.

CONCLUSION
In conclusion, data breaches pose a major risk to both people and businesses. They may expose private financial and personal data, resulting in identity theft and other types of fraud. However, you may lessen your risk of being a victim of a data breach by taking proactive measures to secure your personal information and being alert about internet security. This entails creating strong passwords that are only used by you, updating your software regularly, exercising caution when opening emails or clicking links, keeping an eye on your bank accounts and credit reports, using antivirus and firewall software, being cautious about the information you share online, and using a VPN when using public Wi-Fi networks. You can help safeguard yourself from the risks associated with data breaches by taking these actions.