What is WEB 3.0?
The goal of Web 3.0 is to eliminate reliance on a single
server or database. Web 3.0 sites and programmes will function on peer-to-peer
nodes, blockchains, or decentralized networks. In the coming Web 3.0 era,
virtual assets are expected to become a need.
The basic characteristics of Web 3.0 semantic web are:
- Money
(virtual assets) as a core feature
- New
capabilities brought to users by decentralized applications
- Users’
control over their identities and data
- Self-governance
Through the integration of crypto wallets, which guarantee
anonymity and security, international payments and transactions are made
possible on Web 3.0 websites and apps. Users will have the option to
participate in online communities and use tokens to influence their governance.
Web 3.0 is not a fundamentally different form of the Internet to which the
entire world will transition. Internet 3.0's shift has already begun.
Companies working on Web 3.0 are concentrated on resolving
issues with the Web 2.0 infrastructure. Specifically, the monopoly of IT
behemoths over consumer data ownership. Users are unable to profit from the
information they give tech companies by way of their actions. Content producers
won't have to split earnings with middlemen in Internet Web 3.0. The notion of
Web 3.0 includes discussion of ownership structure development. Web 3.0 on the
internet gives ownership to a lot more parties. It seems certain that Web 3.0
will continue to expand.
Web 3.0 Cybersecurity Features:
Identity Native:
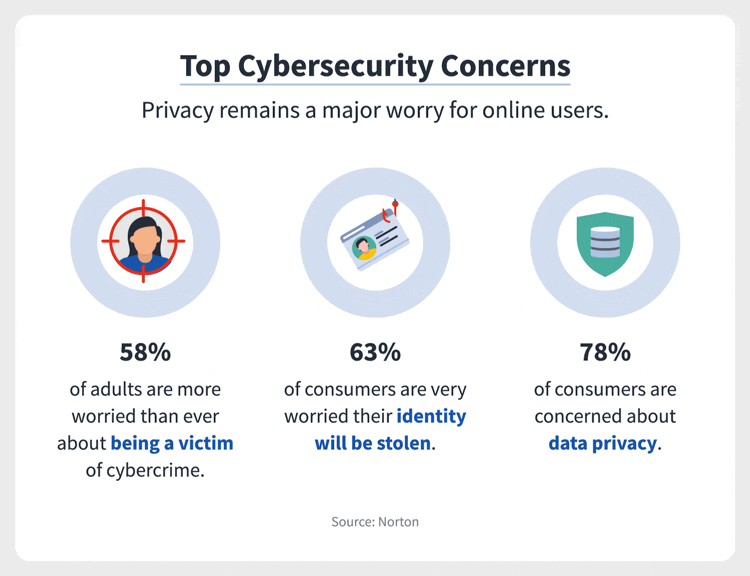
The Web 2.0 era was distinguished by several data breach
scandals. People have little influence over what businesses did with the data
they collected. Data harvesting became a serious problem, and the data centres
run by well-known platforms turned into virtual gold mines of private data
gathered from all over the internet. The degree to which individuals have lost
control over the information on them online was demonstrated by scandals like
the Cambridge Analytica one.
A new strategy is required since it is clear that
centralised solutions cannot ensure privacy or keep data secure. Users own
their data and content in the identity-native distributed application
environment known as Web 3.0. With the use of smart contracts, users may enable
anonymous access to their data and protect their privacy.
Web applications can also utilise reputation metrics
connected to users' digital identities to decide what permissions to provide
users or whether they qualify for participation. In a Web 3.0 era, there should
be fewer high-profile data privacy breaches since there would be less
dependence on central information gatekeepers like huge tech corporations.
Trust less:
The security paradigm of zero trust is getting a lot of
attention in the field of information security. All U.S. government
institutions, including those at the Federal level, must now comply with
particular zero trust network criteria by 2024. The concept of zero trust is
the assumption that nothing on a network can be trusted.
From a Web 3.0 perspective, decentralization shifts the
internet in alignment with something resembling a zero-trust security model. In
the era of Web 2.0, users trusted the companies that owned the websites and
platforms they interacted with online. Instead of data passing through
intermediaries that users trust, Web 3.0 is trustless because data flows
peer-to-peer in decentralized applications (dApps).





0 Comments